Technology Update - Information Security Issue
October 6, 2022
RISING RATE OF RANSOMWARE
YOUR DATA HAS BEEN ENCRYPTED! Pay $2.5 million in Bitcoin for the encryption key. Ransomware is on the rise, but what is it? Ransomware is a type of malware designed to deny a user or organization access to files on their devices until a sum of money is paid. Many organizations in 2022, including some higher education institutions, have been devasted by ransomware. Earlier this year, Lincoln College in Illinois reported their fall enrollment projections were affected after systems supporting recruitment, retention, and fundraising efforts were inoperable due to a ransomware attack. Recently, the Los Angeles Unified School District, which is the second largest district in the United States, was hit with a ransomware attack affecting their food services and business operations.
The FBI, CISA, and other government agencies anticipate attacks may increase as the 2022/2023 school year begins. The best defense against ransomware is to maintain offline backups of data, keep all operating systems, software, and firmware up to date, and use multifactor authentication (MFA) for all services to the extent possible.
October is National Cybersecurity Awareness Month. To celebrate, join our Chief Information Security Officer, Dr. Pablo Molina, and his colleagues for an interactive session on How to Become a Cyber Secure Dragon. Use your Drexel credentials to access this session at https://drexel.zoom.us/my/doctorp on Thursday, October 13th at 11:00 AM.
We are also giving away swag to students who have completed the Drexel University Security Training (D.U.S.T.) between April 1, 2022, and October 25, 2022. To receive your swag, you must complete the DUST training and bring your 'certificate of completion' on your mobile device or a hard copy to our table by the Mario Dragon Statue on October 25, 2022, from 12 pm to 2 pm. To sign up for training, email informationsecurity@drexel.edu.
MFA FATIGUE
Multi-factor authentication is still a best practice to use for securing your accounts. But there is a new social engineering attack aimed at bypassing MFA on accounts. This tactic is known as MFA fatigue, and it’s being used by bad actors to gain access to organizations’ networks. Some recent breaches in which this tactic was used are Uber, Cisco, Microsoft, etc.
This is how it works. A bad actor obtains a user’s compromised account credentials and attempts to log in to the compromised account, which then sends an MFA authorization request to the user. This process is repeated frequently until the user gets so annoyed with the requests; they accept them just to stop the notifications. Occasionally, the bad actor might contact the compromised user, during the attack, pretending to be the IT department and convince the user the only way to stop the requests is to just click accept. Once a false MFA request is accepted by the user, bad actors can gain access to the compromised accounts and work their way into the organization’s network.
If you think you’re experiencing this type of attack, we recommend the following:
- Don’t accept requests you don’t initiate, don’t match your location, or seem suspicious.
- Click decline and report it in the app.
- Immediately contact us at informationsecurity@drexel.edu.
SOMETHING’S PHISHY…
Job scams are growing and some result in financial losses. These scams come in a variety of forms, such as fictitious government or postal jobs, mystery shopper(s), a staffing or temp agency, or even a recruiter who requires a fee for their services. Scammers have also posted imitations of a trusted organization’s job posting on reputable job search sites, such as LinkedIn, Indeed, etc. as well as created an imitation of a trusted organization’s website with a job posting. Remember, legitimate organizations will not require you to purchase start-up equipment, pay upfront for background screenings, send employment contracts requesting Personal Identifying Information before you are hired, or contact you using non-company email domains or teleconference applications. For more information on job scams, including warning signs and recommendations for employers and job seekers, check out our Student Job Posting Scams webpage, the FBI’s Public Service Announcement from earlier this year, and the FTC’s Job Scam article.
In the coming weeks, we will be deploying a phishing simulation for all our faculty and staff members. Don’t let scammers reel you in with their grandiose statements, scare tactics or impersonations of a trusted organization or contact. Phishing scams often impersonate a legitimate organization or contact and lure you into providing sensitive information, e.g., username, password, social security number, etc. These scams are becoming more sophisticated and targeted. Obvious indicators, such as spelling and grammatical mistakes, are not seen as much. Many students, staff, and faculty, including some at Drexel University, fall for these scams and lose thousands of dollars and/or have their identities stolen.
For more information and to learn how to protect yourself from phishing scams, visit our Debunking Email Scams and Best Practices webpages. Remember “All That Glitters Is NOT Gold”! If you suspect you received a phishing message in your Drexel email account, please report them to us using either of the following methods:
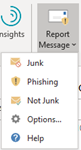
Using the Outlook desktop application’s “Report Messages” button:
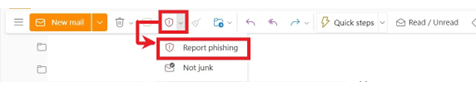
Or use the Outlook web application’s toolbar above the email message:
WHAT DRAGONS CAN DO
D - Don’t click links or download attachments for unsolicited emails.
R - Recognize and report phishing.
A - Always keep your systems and software up to date.
G - Go enable multifactor authentication (MFA) when possible.
O - Or if not possible, always use strong unique long passwords for your accounts.
N - Not to forget, complete the Drexel University Security Awareness Training (DUST).
S - Save your data by backing it up externally. Drexel OneDrive provides 5TB of storage space.
PASSWORD-LESS AUTHENTICATION
In the coming weeks, Drexel will enable Microsoft’s Password-less authentication for accounts. Password-less authentication uses number matching in the Microsoft Authenticator App to allow MFA-enabled users to log into Office 365 without entering a password. When going through the authentication process, you will be presented with a number that must be entered in the Authenticator app to complete the authentication.

To set up, follow the steps below (if you already have the Microsoft Authenticator App installed skip to step 5):
- Browse to https://aka.ms/mysecurityinfo.
- Sign in, then click Add sign-in method > Authenticator app > Add to add the Authenticator app.
- Follow the instructions to install and configure the Microsoft Authenticator app on your device.
- Select Done to complete Authenticator app configuration.
- In the Microsoft Authenticator app, choose Set up phone sign-in from the drop-down menu of your Drexel.edu account.
- Follow the instructions in the app to finish registering your account and device for password-less phone sign-in.
ANOTHER ONE BYTES THE DUST
Get the knowledge you need to protect yourself and others against cyber threats such as phishing and job scams. Take the D.U.S.T. training and receive your SANS security training certificate! To request access to this training, students should email informationsecurity@drexel.edu. Faculty and staff can access the training via Career Pathway in DrexelOne.
Information Security Resources
To stay informed about cybersecurity news, common scams, FAQs, and other information, visit the Drexel Information Security website at https://drexel.edu/it/security.
For tips on information security while learning and working remotely, please visit the Information Security Best Practices webpage.
Report any cybersecurity incident to informationsecurity@drexel.edu.