Technology Update - Information Security Issue
October 6, 2020
OCTOBER IS NATIONAL CYBERSECURITY AWARENESS MONTH
Do not be tricked into treating scammers and hackers to your information. Phishing, COVID, text messages, and social engineering scams rise. Many people, including some at Drexel University, fall for online and phone scams every year. Let us be aware. The best defense against these cyberattacks is to exercise your critical thinking and to take the Drexel University Security Training.
Learn more about these topics by attending an information security talk by Drexel University's Chief information Security Officer, Dr. Pablo Molina on October 22nd at 6:00 PM. The International Graduate Student Association (IGSA) and the Women in Computing Society's (WiCS) invite all faculty, staff, and students to attend by registering via Zoom.
Gone phishing?
Phishing email messages often impersonate a legitimate organization and lure you into providing sensitive information, e.g., username, password, security number, etc. They can have a strong sense of urgency, lack detail, have outlandish requests, demand action, and contain spelling errors. Check out some examples on our Debunking Email Scams webpage. If you receive phishing messages in your Drexel email account, please report them.
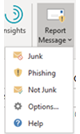
Report these messages with the Outlook desktop application's "Report Messages" button:
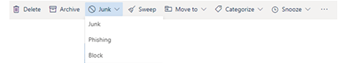
Or use the Outlook web application's tool bar above the email message:
Cybersecurity Maturity Model Certification (CMMC) & National Defense Authorization Act Section 889 (NDAA 889)
CMMC and NDAA 889 are new regulations designed to ensure the protection of information and reduce the risk of data leakage in the Defense Industrial Base supply chain. The CMMC measures an organization's security posture. This new certification has five levels, requires a third-party assessment, and is required for all organizations doing business with the DoD. This new certification means that some Drexel University researchers will have to obtain a specific certification level to bid and receive awards for select contracts.
The National Defense Authorization Act Section 889 (NDAA 889) "prohibits executive agencies from entering into, or extending or renewing, a contract with an entity that uses any equipment, system, or service that uses covered telecommunications equipment or services as a substantial or essential component of any system, or as critical technology as part of any system, on or after August 13, 2020, unless an exception applies or a waiver is granted".
As of today, NDAA 889 proscribes telecommunications and video surveillance equipment and services produced or provided by the following companies, their subsidiaries and affiliates: Huawei Technologies Company, ZTE Corporation, Hytera Communications Corporation, Hangzhou Hikvision Digital Technology Company, and Dahua Technology Company.
Federal government organizations already requested that Drexel University certify compliance with NDAA 889 before paying the tuition of government employees or fees to recruit students on campus. Most likely, federal research contracts will incorporate similar clauses soon. Purchasing equipment and services from these vendors could jeopardize Drexel's ability to receive federal funding.
ANOTHER ONE BYTES THE DUST
Students, faculty, and staff can byte the D.U.S.T.: Drexel University Security Training. In this training participants learn how to protect against cyberthreats and receive a SANS security training certificate upon completion. To request access to this training, students should email informationsecurity@drexel.edu. Faculty and staff can access the training via Career Pathway in DrexelOne.
Information Security Resources
To stay informed about cybersecurity news, common scams, FAQs, and other information, visit the Drexel Information Security website at https://drexel.edu/it/security.
For tips on information security while learning and working remotely, please visit the Information Security Best Practices webpage.
Report any cybersecurity incident to informationsecurity@drexel.edu.